Is your AI a leak or a vault?
In 2024, the priority was AI capability. In 2026, the priority is AI integrity. As businesses move from basic chatbots to integrated AI Agents that handle sensitive CRM and financial data, a new risk has emerged: the AI Privacy Gap.
You cannot leverage the full power of a Large Language Model (LLM) if you are constantly worried about where your data goes. At Nuclay, we treat privacy as the foundation that makes AI scalable, not a hurdle that slows it down.
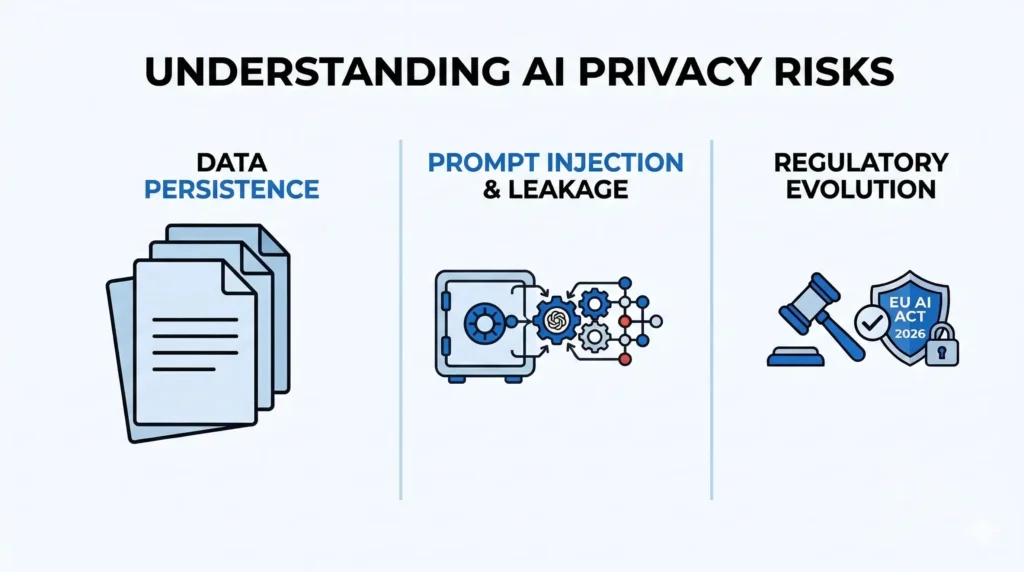
Understanding the AI Privacy Risks
Traditional data privacy focuses on who can access a file. LLM privacy is more complex because it involves how a model “learns” and “processes” information.
The three primary risks for businesses today:
- Data Persistence: If you use a public LLM to summarize a private contract, that data leaves your servers. It may be used to train future versions of the model, potentially exposing your trade secrets to competitors through their own prompts.
- Prompt Injection & Leakage: Without proper guardrails, a sophisticated user could “trick” an AI into revealing sensitive backend information or proprietary logic used in the system’s instructions.
- Regulatory Evolution: With the EU AI Act and new global privacy statutes fully active in 2026, “unintentional data usage” is no longer a valid legal excuse. Companies are now legally responsible for the data lifecycle within their AI ecosystems.
Technical Solutions for Data Security
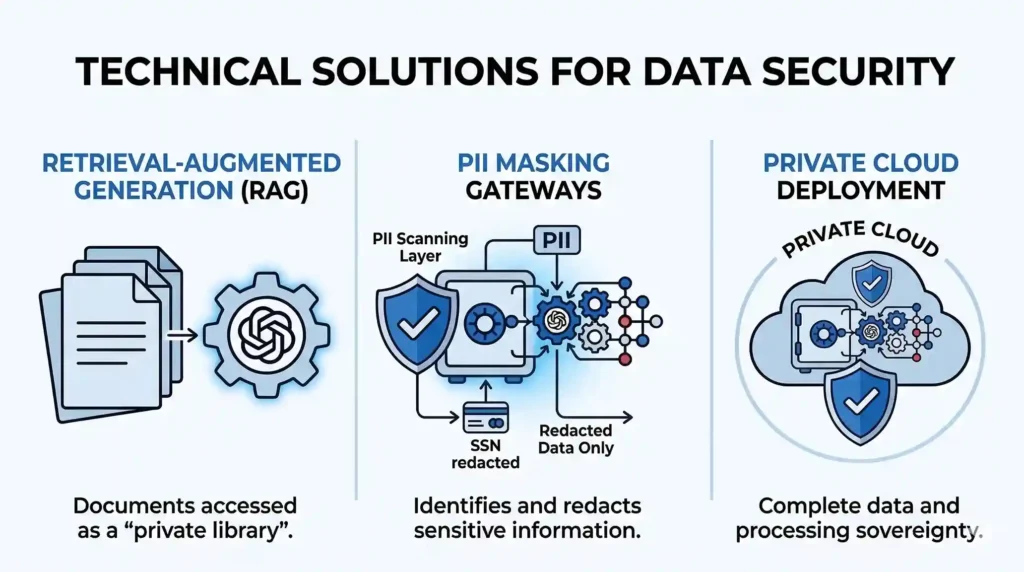
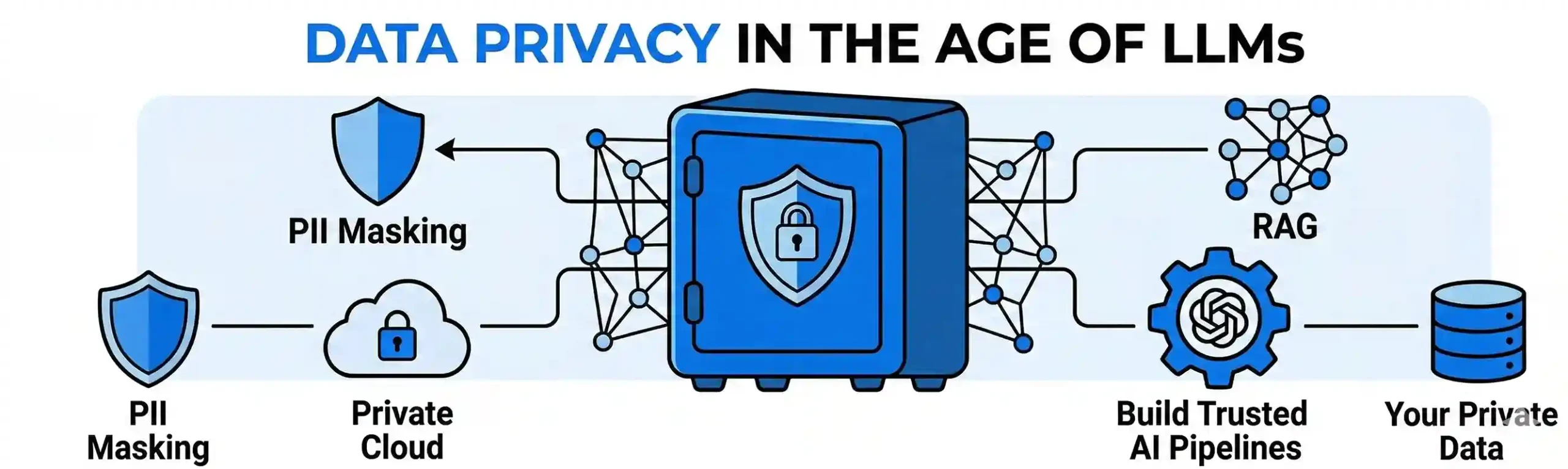
To use AI safely, businesses must move away from public web-chat interfaces and toward Private AI Infrastructure. We implement three core technologies to ensure your data stays yours:
1. Retrieval-Augmented Generation (RAG)
Instead of “teaching” a model your secrets via fine-tuning (which makes the data part of the model’s permanent memory), we use RAG. The AI is given temporary access to a “private library” of your documents. It reads the relevant file, answers the specific query, and then the context is cleared. Your data remains in your secure vault; only the answer is generated.
2. PII Masking Gateways
We build automated “Gatekeepers” between your team and the AI. Before a prompt reaches the LLM, a scanning layer identifies and redacts Personally Identifiable Information (PII)such as social security numbers, private keys, or client names. This ensures that even if a model provider experiences a breach, your sensitive data was never sent to them in the first place.
3. Private Cloud Deployment
For maximum security, we deploy models within your own private cloud environment (AWS, Azure, or GCP). This creates a “Closed Loop” where the data, the model, and the processing power all live within your company’s existing security perimeter. Not even the AI provider can see the interactions.
Privacy as a Competitive Advantage
Most organizations are moving slowly because they are paralyzed by security concerns. By building Privacy by Design, you remove that friction.
When your backend architecture is verified as secure, you can deploy AI agents across every department from HR to Finance without risk. In 2026, the most successful companies aren’t just the ones with the smartest AI; they are the ones with the most trusted data pipelines.
Secure Your AI Strategy
Your proprietary data is your most valuable asset. In the race to automate, you shouldn’t have to choose between innovation and security.
At Nuclay Solutions, we specialize in building the bridges and vaults that allow your business to use the world’s most powerful LLMs with total peace of mind. We turn privacy into a strategic asset that allows you to move faster than the competition.
Secure Your Proprietary Data.
Stop data leaks. Build your private AI vault today.
Discuss AI Strategy